
OneLogin Warns of Breach at U.S. Data Center
Security firm OneLogin, which provides single sign-on and other identity and authentication products, has suffered a data breach that it says likely affects all of

Security firm OneLogin, which provides single sign-on and other identity and authentication products, has suffered a data breach that it says likely affects all of

In a new study out from a UK based research team, scientists have discovered an inexpensive and easy-to-use way to validate the authenticity of any

Congressional leaders are continuing to pressure federal agencies to address shortcomings in the security of the telecommunications infrastructure, specifically to warn consumers about weaknesses that

A few days after LastPass released a fix for some critical security flaws in its extensions for Chrome and Firefox, a researcher has identified a
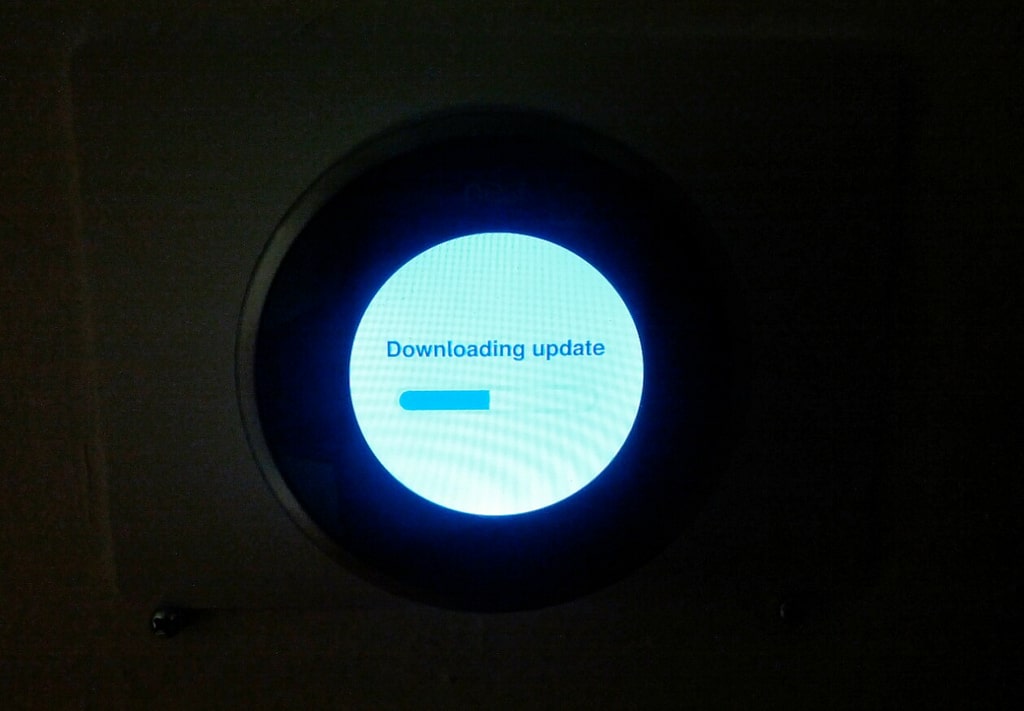
Nest, maker of smart home thermostats and other devices, is adding two-step verification to its authentication process, making it more difficult for attackers to take

It’s that time of year again, when the security industry looks westward with a mixture of anxiety, dread, and expense-account induced giddiness: RSA week. When

Lavabit, the secure email service that shut down in 2013 rather than turn over the encryption key for a user account to the federal government, has

Attackers backed by a foreign government were behind the attack that compromised health insurance company Anthem in 2015, a breach that compromised the information of more

The fraud schemes that consumers and businesses face every day are the end result of a lot of research, work, and planning on the part