Security Professionals Expect More Attacks On IIoT in 2017

As technology vendors race to create more and more devices connected to the Internet of Things (IoT) the opportunity for hackers to get into these devices grows larger and larger, as these IoT devices are usually made with little to no regard for security. The fears of a large-scale attack waiting to happen were solidified this week when security firm Tripwire released the […]
Nest Adds Two-Step Verification for Users
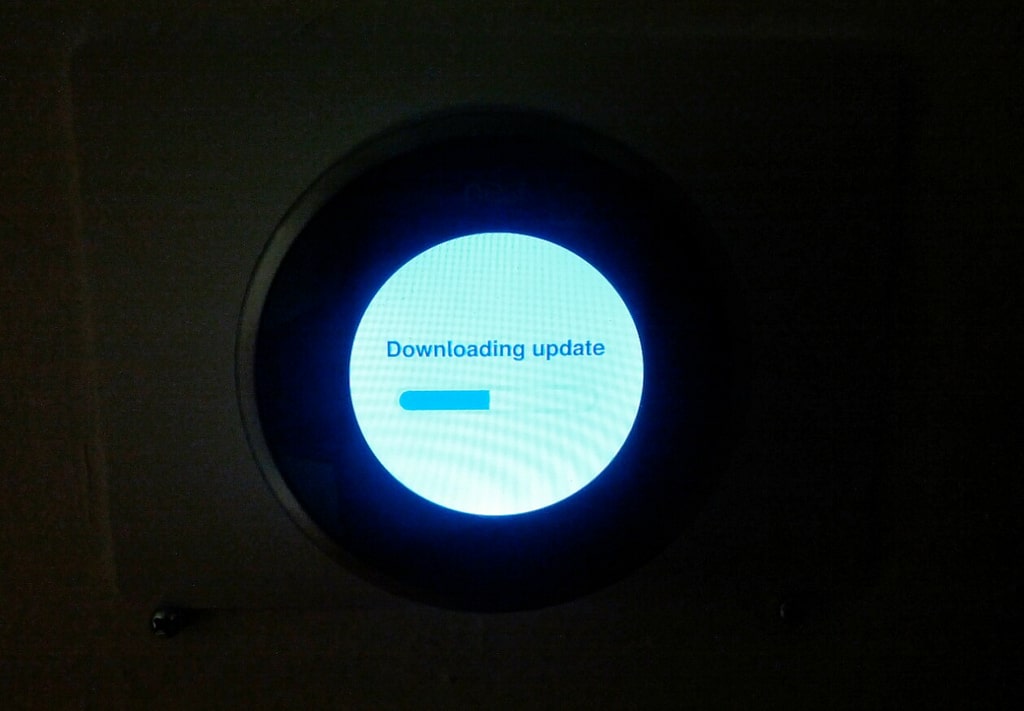
Nest, maker of smart home thermostats and other devices, is adding two-step verification to its authentication process, making it more difficult for attackers to take over users’ devices. The company said on Tuesday that it is implementing the ability for users to require a short code sent by SMS as part of the sign-in process […]
‘When Computers Start Killing People, There Are Going to Be Consequences’

SAN FRANCISCO–The massive, rapidly expanding network of insecure IoT devices is becoming so large and unwieldy that it will inevitably attract attention from government regulators in the near future. And that’s actually a positive development, security experts say. “As everything becomes a computer, computer security becomes everything security. The beachhead of all of this is […]
FDA Sets Guidance on Medical Device Security

The Food and Drug Administration has published new recommendations for both manufacturers and regulators on how to deal with security for medical devices, including implantable devices. Calling device security a shared responsibility, the FDA guidance focuses on the postmarket cybersecurity issues, such as vulnerability response and remediation. The new document is not a set of regulations, but […]
House Lawmakers to Look at Mirai Botnet DDoS Attacks

A pair of House subcommittees are planning to hold a joint hearing to look at the role that IoT devices have played in a number of recent DDoS attacks. Much of the high-profile DDoS activity that’s taken place lately has been attributed to the Mirai botnet, a series of networks made up of compromised embedded devices. […]
IoTSeeker Scanner Finds Smart Devices With Dumb Credentials

With the Mirai botnet still wreaking havoc, and other IoT botnets appearing, security researchers are looking for ways to discover the insecure devices that are being targeted by attackers before they can be compromised. One such effort is a new scanner that will check networks for devices that are using default credentials, which often are exploited […]
On the Wire Podcast: Mike Mimoso

In a remote episode of the podcast, Dennis Fisher talks with Mike Mimoso of Threatpost about the sessions from the Security Analyst Summit in Tenerife, Spain. The discussion touches on IoT security, the security development lifecycle, and whether device security will improve anytime soon.
Time is Now For an IoT Security Development Lifecycle

TENERIFE–Microsoft engineers, executives, and developers have spent much of the past decade spreading the gospel of the security development lifecycle (SDL), trying to convert people and organizations to the religion of building security into software and other products from the beginning of the process. That effort has succeeded in many ways, and now experts say […]