Pindrop® Pulse, First to Accurately Detect Deepfakes from OpenAI’s Voice Engine
Several of our customers have asked Pindrop if our recently launched deepfake detection product, Pindrop® Pulse, can detect synthetic content generated by OpenAI’s1 new Voice
4 Top Cybersecurity Trends Discovered From Our Recent CFX Event
Ensuring cybersecurity is front and center for companies is now a non-negotiable task. That’s why Pindrop released quarterly insider sessions to check in and ensure
Pindrop Named A Winner in the FTC Voice Cloning Challenge
The FTC (Federal Trade Commission) held its sixth Voice Cloning Challenge under the America COMPETES Act to drive innovation in voice cloning detection for protection
View by category
Popular Blogs
On the Wire Podcast: Samy Kamkar
Samy Kamkar spends a lot of time coming up with clever hardware hacks, and his latest project, PoisonTap, may be at the top of the

Carbanak Gang Calling Hotels to Convince Victims to Install Malware
The Carbanak gang, one of the more successful and prolific cybercrime groups at work today, is using a new tactic to get its malware onto

Lawmakers Ponder Regulatory Remedy for IoT Security
The recent DDoS attacks by the Mirai botnet against various targets, including DNS provider Dyn, have drawn the attention of congressional leaders, who say there may

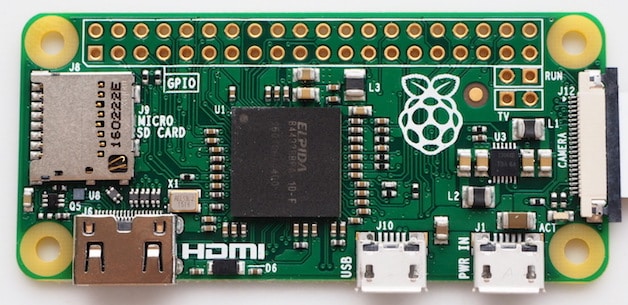
PoisonTap: The Tiny Internet-Hijacking, Cookie-Stealing, Backdoor-on-a-Board
A renowned hardware hacker has released a cheap USB device that, when plugged in to any computer–even password-protected or locked ones–can hijack all of the

EPIC Sues FBI Over Biometric Database Records
A major privacy group has filed a lawsuit against the FBI to force the bureau to release all relevant documents about its plan to share

Google, Facebook, Twitter Ask Trump to Protect Strong Crypto
A group of powerful technology vendors and Internet firms, including Google, Twitter, Uber, Amazon, and Facebook, have sent a letter to Donald Trump’s transition team

Researchers Warn of BlackNurse Low-Volume DDoS Attacks
The recent wave of high-profile DDoS attacks against hosting providers, telecoms, and other targets have been among the most powerful ever seen, but researchers say

Mozilla to Enforce Content Security by Default in Firefox
One of the many ways that attackers use to get their malicious code onto users’ machines is by using drive-by downloads. They often will compromise

Yahoo Data Breach May Have Been Identified in 2014
Some Yahoo employees were aware that the company had been compromised as far back as 2014, even though Yahoo officials only disclosed the breach affecting
Pindrop’s Phoneprinting Technology Addresses the $400 Million Fraud Problem
Analysts at Aite Group have identified five key security and service steps that legacy solutions are failing to perform. These are the features that are
