Pindrop® Pulse, First to Accurately Detect Deepfakes from OpenAI’s Voice Engine
Several of our customers have asked Pindrop if our recently launched deepfake detection product, Pindrop® Pulse, can detect synthetic content generated by OpenAI’s1 new Voice
4 Top Cybersecurity Trends Discovered From Our Recent CFX Event
Ensuring cybersecurity is front and center for companies is now a non-negotiable task. That’s why Pindrop released quarterly insider sessions to check in and ensure
Pindrop Named A Winner in the FTC Voice Cloning Challenge
The FTC (Federal Trade Commission) held its sixth Voice Cloning Challenge under the America COMPETES Act to drive innovation in voice cloning detection for protection
View by category
Popular Blogs

Tor Browser Adds Sandbox
The newest release of the Tor browser for Linux now include a sandbox, which is designed to make it more difficult for attackers to exploit

The Weird and Wild Stories of 2016
There are any number of adjectives one could employ to describe 2016, most of which can’t be printed here. One of the gentler descriptors we can
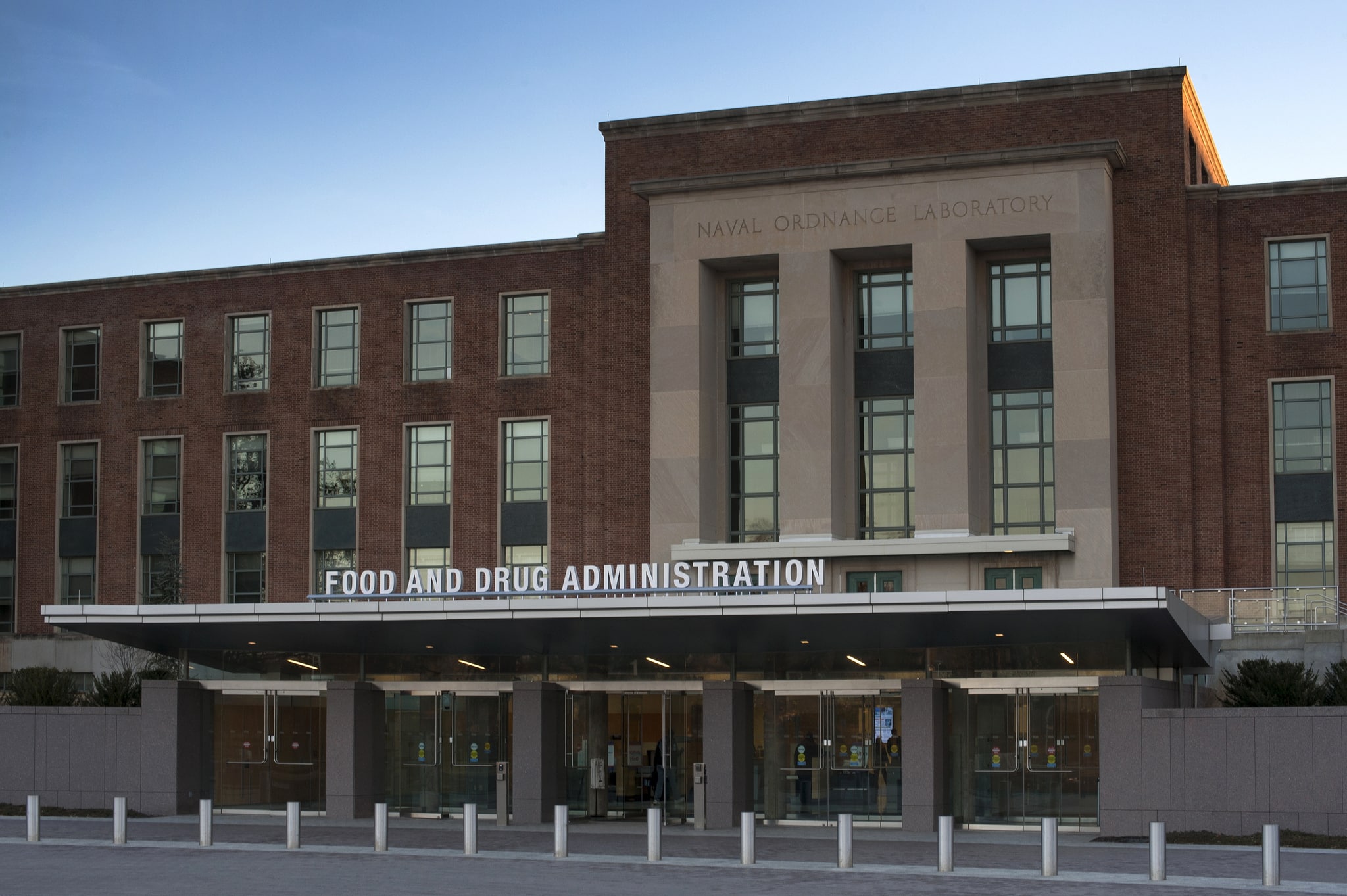
FDA Sets Guidance on Medical Device Security
The Food and Drug Administration has published new recommendations for both manufacturers and regulators on how to deal with security for medical devices, including implantable devices.

2016: Maybe Everything Wasn’t Completely Terrible
Let’s face it: 2016 has been pretty rough year. Things didn’t go all that well for humans in the last 12 months, and computers didn’t
Assessing Phone Fraud in the Contact Center: Best-In-Class Solutions
Contact center fraud loss is expected to double from $393M to $775M by 2020. Despite the intent to administer positive and timely customer experiences, contact

New Leet Botnet Generating Huge DDoS Floods
A new botnet that is capable of some of the larger DDoS attacks ever seen has emerged in the last few days, launching floods of

Critical Vulnerability Haunts Popular PHP Library
There’s a critical security vulnerability in the PHPMailer library, a flaw that could allow an attacker to execute arbitrary code. The bug can be exploited

Apple Delays Requirement for App Transport Security
Apple has pushed back a deadline for developers to support a key transport security technology in apps submitted to the company’s app stores. Officials said

Call Centers a Soft Target for Fraudsters
The fraud schemes that consumers and businesses face every day are the end result of a lot of research, work, and planning on the part

House Working Group Says Don’t Weaken Encryption
In a year-end report, a key congressional working group on encryption said that any governmental initiative to backdoor encryption systems is against the interests of
