ST. MAARTEN–Researchers investigating modern cyber espionage operations have found a direct link between the Moonlight Maze attacks that hit a number of United States military and government agencies in the 1990s and operations that are still ongoing today. The connections, through code samples, logs, and other data, show that some of the same tools and infrastructure used 20 years ago are still in use by advanced attackers right now.
The Moonlight Maze attacks were among the first major cyber espionage campaigns to gain public attention, and security researchers often point to the attacks as the beginning of the modern advanced threat era. The attacks went on for years and included highly complex techniques and the exfiltration of a huge amount of data. Researchers at Kaspersky Lab, working with counterparts from King’s College London, recently discovered that a backdoor used by the Moonlight Maze attackers in 1998 also has been used by the Turla APT attack group, possibly as recently as this year. The new details come from a months-long analysis of data and logs from a server that was compromised during the Moonlight Maze attacks and preserved by a systems administrator since then.
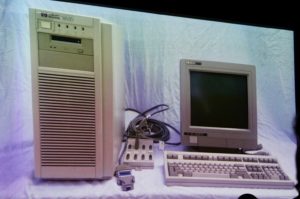
The original Moonlight Maze attackers mainly used Unix and had a large set of tools at their disposal. They were targeting Solaris systems for the most part and had a custom backdoor that they used often. One of the systems that they compromised was a server known as HRtest (pictured below), which administrator David Hedges has kept. Hedges allowed Kaspersky’s researchers and Rid access to the server, including access logs, the attackers’ own logs, and an extensive toolset used by the attackers, including 43 separate binaries. The researchers discovered that the attackers had made a key mistake in some of their operations.
“In the late 1990s, no-one foresaw the reach and persistence of a coordinated cyberespionage campaign.”
“It was their standard behavior to use infected machines to look for further victims on the same network or to relay onto other networks altogether. In more than a dozen cases, the attackers had infected a machine with a sniffer that collected any activity on the victim machine and then proceeded to use these machines to connect to other victims. That meant that the attackers actually created near complete logs of everything they themselves did on these systems—and once they did their routine exfiltration, those self-logs were saved on the HRTest node for posterity. The attackers created their own digital footprint for perpetuity,” Kaspersky said in a post detailing their findings, which were announced at the Security Analyst Summit here Monday.
The information that Hedges gave the researchers, along with other data they had collected over the years during investigations into the Turla APT campaigns, allowed them to dig in and connect the Moonlight Maze operation to the Turla attacks. The analysis shows that the tools used by the attackers have evolved over the years, as needs have dictated, and have used a wide range of tools and techniques.
The connection between the old Moonlight Maze attacks and techniques and the recent Turla campaigns is a solid one, but the researchers stopped short of saying that the attackers themselves are the same.
“An objective view of the investigation would have to admit that a conclusion is simply premature. The unprecedented public visibility into the Moonlight Maze attack provided by David Hedges is fascinating, but far from complete. It spans a window between 1998-1999 as well as samples apparently compiled as far back as late 1996. On the other hand, the Penquin Turla codebase appears to have been primarily developed from 1999-2004 before being leveraged in more modern attacks,” the researchers said.
The data that the researchers had gave them the ability to look at complete sessions between the attackers and proxies, target systems, and other machines from nearly 20 years ago. That gave them detailed insight into the attackers’ techniques.
“This looks nothing like a modern APT,” Kaspersky researcher Juan Andres Guerrero-Saade said during the talk Monday.
Image: Aaron Harmon, CC by license.


