
Android Trojan Spreads Through Fake Cell Towers
Attackers in China are using rogue cell base stations to spread versions of an Android banking Trojan that steals user credentials and has the ability

Attackers in China are using rogue cell base stations to spread versions of an Android banking Trojan that steals user credentials and has the ability

Google has rolled out several new security features for its G Suite and Google Cloud Platform, including a DLP system that finds and redacts sensitive
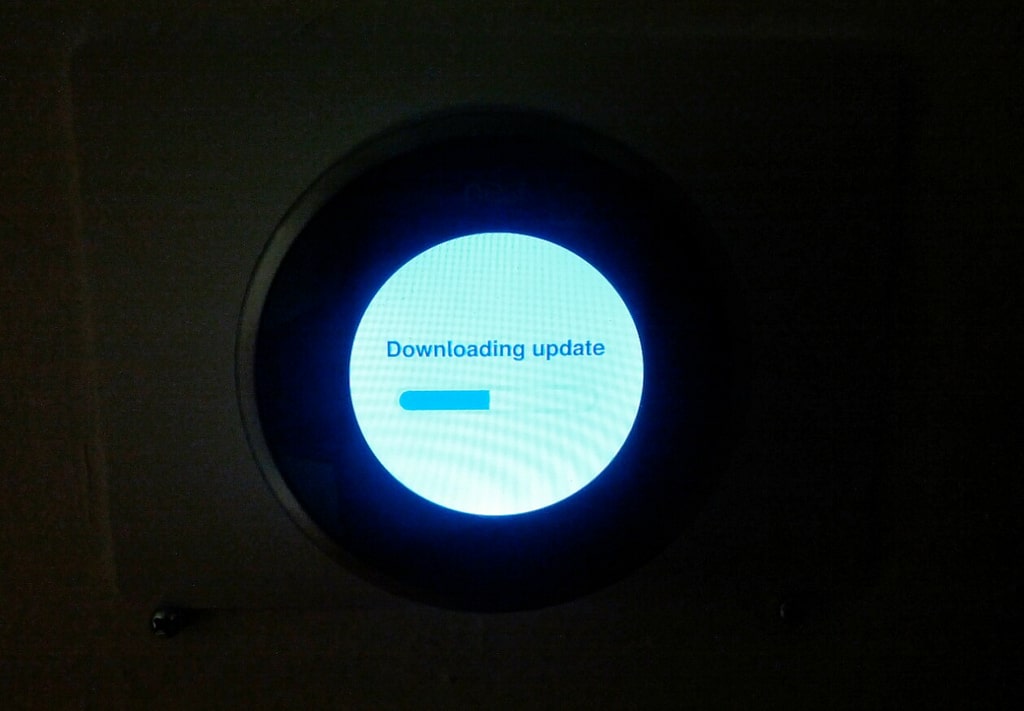
Nest, maker of smart home thermostats and other devices, is adding two-step verification to its authentication process, making it more difficult for attackers to take

SAN FRANCISCO–Artificial intelligence and machine learning are the two dominant buzzphrases at the RSA Conference this year, but some of the founding fathers of the

OAKLAND–Google is making a pair of changes to its hosted G Suite Gmail service for enterprises to enhance the security of the service. The most

OAKLAND–WhatsApp has enjoyed tremendous growth in the last couple of years, a trend that accelerated even further when the company announced it was implementing end-to-end

OAKLAND–The security industry as a whole is really good at identifying interesting new problems and coming up with fancy products to solve them. But there is still

OAKLAND–Facebook has developed a new account-recovery system that eschews the typical communications channels used for this process, and instead relies on a user’s connections with other

Lavabit, the secure email service that shut down in 2013 rather than turn over the encryption key for a user account to the federal government, has